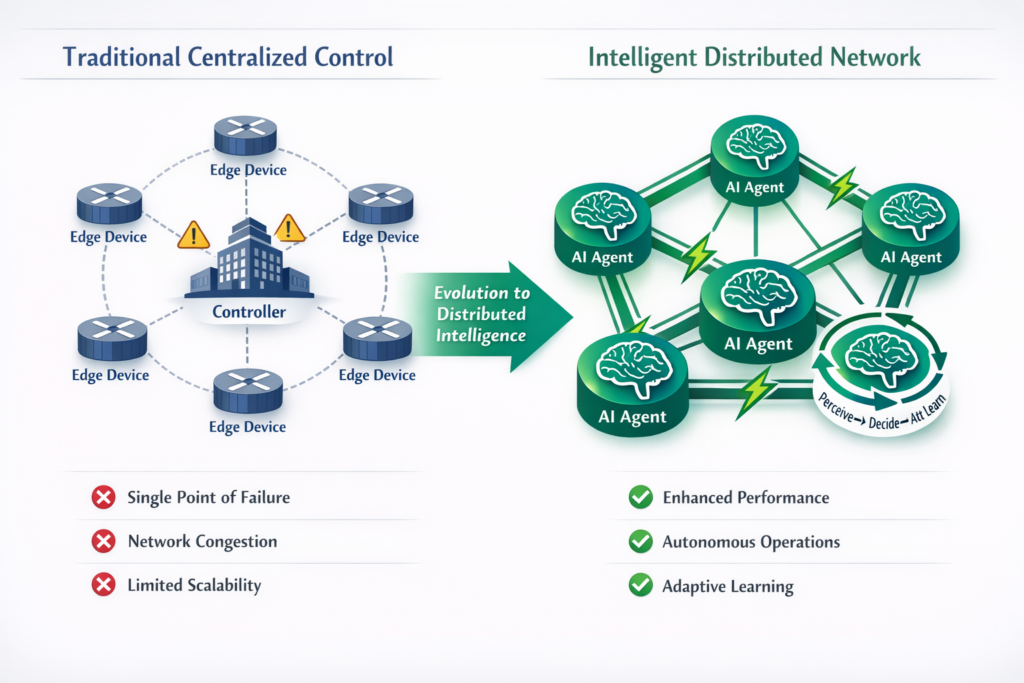
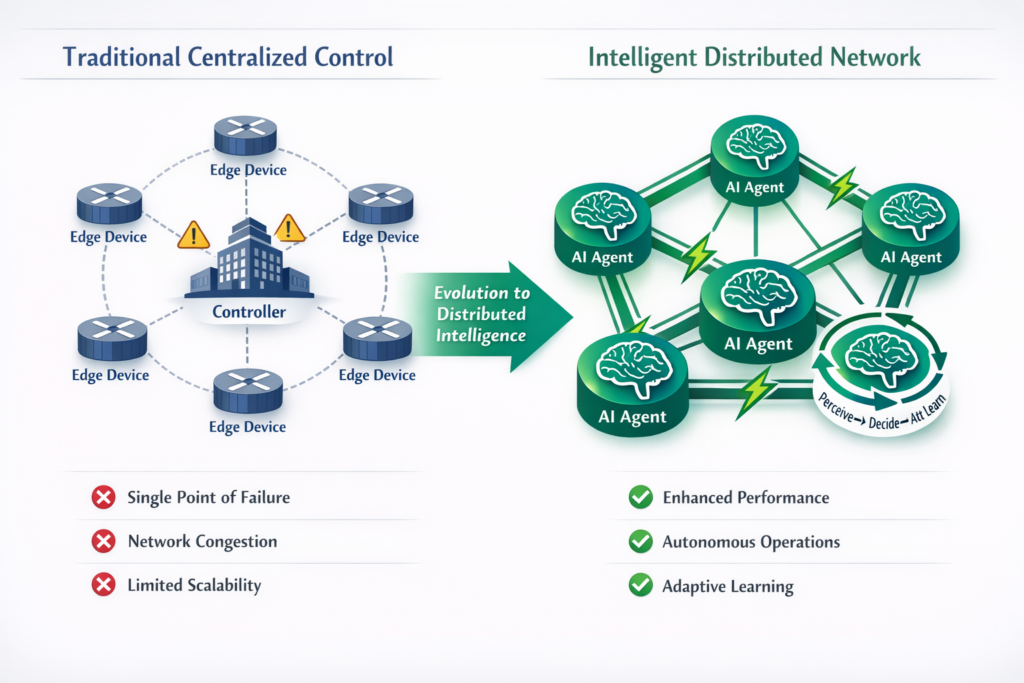
In my previous exploration of making SD-WAN smarter with MCP, we examined how edge compute optimizes network performance by processing data closer to where it is generated. But when you have a modern enterprise network—especially one with hundreds or even thousands of sites—you’ve probably hit the same wall everyone else has: there’s just too much happening, too fast, for centralized, human-driven decision-making to keep up.
Why has centralized control hit its ceiling?
In traditional SD-WAN architecture, there’s a distinct separation of duties:
- A manager for handling administration
- A controller for handling the routing aspect
- An orchestrator for overseeing security onboarding of devices at the edge of the network.
This model has been quite effective and can support thousands of edge devices of enterprise networks worldwide. But by its nature, this introduces a delay I call the “latency of logic,” the time between recognizing a network problem and implementing a solution.
Let’s examine a typical case. When the transport connection at a satellite retail location begins to deteriorate, here’s what happens:
- The performance problem is detected by an edge device via telemetry.
- Telemetry data streams to the central controller, which can involve several network hops.
- The controller evaluates conditions against predefined policy templates.
- A new routing policy is introduced and verified.
- The changes in configuration are sent to the edge device.
- Forwarding tables in local networks are updated.
Although this is effective in stable environments, in the fast-paced world that we have today, with minute-by-minute changes in traffic flow, link quality that fluctuates unpredictably, and applications that have changing real-time needs, this is now the bottleneck.
The future belongs to networks where intelligence is distributed, decisions are local, and the network itself becomes a collection of autonomous agents working in concert.
A new paradigm: Networks as distributed intelligence
Imagine a network where each edge device isn’t just a forwarding node, but an intelligent agent that can perceive, reason, and act. These agents operate continuously:
Perception → Decision → Action → Learning
Each agent observes its local environment through real-time telemetry, understands the wider network structure through advanced learning techniques, makes routing decisions instantly, and improves over time. When a link degrades or traffic patterns change, the agent reacts immediately, using local intelligence informed by global knowledge instead of waiting for a distant controller.
To achieve true autonomy, we need to rethink where intelligence exists in the network. The solution lies in AI-driven designs that place decision-making directly at the network edge.
Three pillars of the intelligent network
-
Autonomous decision-making at the edge
This first pillar moves intelligence from distant data centers to the edge. Rather than waiting for a round trip to a central controller for every decision, these devices are now independent agents that understand their own conditions and the bigger picture of the network.
These agents use sophisticated AI that understands network topology as interconnected relationships, not isolated data points. They see not just individual link states, but how congestion propagates, how flows compete for resources, and how decisions ripple through the network.
When the branch office loses connectivity with the central controller, the local agent doesn’t simply shut down. It continues to optimize traffic, enforce policies, and ensure security based on its learned understanding of operational intent.
It is much like moving from a command-and-control model, as used in the military, to the concept of special forces, where every operative has the training and the autonomy to take decisions in the field, with the overarching objective in mind.
2. Learning networks: From rules to rewards
The second pillar is the use of learning frameworks instead of rule-based systems. Traditional SD-WAN relies on fixed thresholds: “If latency exceeds X, do Y.” These rules break down when optimal isn’t a static number, it’s a constantly shifting target.
Machine learning upends this paradigm. Rather than operating according to a set of strict rules, they follow a reward structure that corresponds to business objectives. They try different approaches to routing, see which ones work best, and through a process of learning, understand the idiosyncrasies of your network – for instance, the early morning rush on Circuit A or the evening rush on Circuit B, and the subtle indicators that point to a change in traffic patterns.
The network not only responds, but also anticipates. It learns to take proactive measures, rerouting traffic before problems occur, rather than waiting for thresholds to be crossed.
3. Intent-driven networks: Bridging business and technology
The third pillar bridges the divide between business requirements and technology implementation. When a stakeholder says “video conferencing must work flawlessly” or “POS transactions are always priority,” the network should understand and execute, not wait for engineers to translate intent into technical policies.
Natural language processing as translation layer
Modern AI bridges this gap, acting as an intelligent translation layer that converts high-level business intent into executable technical policies.
For instance, the business intent: “Ensure maximum bandwidth is allocated to point-of-sale transactions during peak shopping hours (10 AM to 8 PM) in all retail outlets” becomes:
- Rules for classifying traffic based on the application signatures of POS.
- Dynamic bandwidth reservation policies that are operative during the given hours.
- Automatic path selection to favor the fastest paths for classified traffic.
- Failover policies to ensure secondary paths are at minimum bandwidth.
- Telemetry collection focused on POS transaction success rates and response times
Business stakeholders won’t see ACLs or QoS policies. They see: “POS transaction intent: Active and Compliant.”
Continuous assurance loop
Once deployed, the agent continuously verifies that network behavior matches stated intent. When drift occurs – a link failure, competing traffic, or changing conditions – the network self-corrects automatically to maintain business objectives.
The tomorrow that’s possible today: Multi-site retail
To put these ideas into context, think about a large retail chain with over 500 locations, each with:
- Point-of-sale systems needing consistent low-latency connections.
- Inventory management systems requiring periodic data transfers.
- Security cameras streaming to central monitoring.
- Customer WiFi with unpredictable usage.
- Seasonal traffic changes (holiday shopping, regional events).
The challenge:
During a busy sales event, multiple stores see traffic spikes. WiFi usage rises as customers check prices online. Inventory systems pull real-time stock data. Security camera traffic increases with more customers. Meanwhile, POS transactions need to maintain sub-100ms response times to generate revenue.
In a traditional centralized SD-WAN:
- Each location reports performance dips independently.
- A central controller processes over 500 telemetry streams.
- An administrator receives hundreds of alert notifications.
- Manual or semi-automated policies are implemented at each location.
- Response times can take minutes, risking missed transaction opportunities.
With distributed AI agents:
Each store’s edge device runs an independent agent that:
- Sees the local traffic surge through real-time analysis.
- Decides to prioritize POS traffic by slowing down bulk inventory updates and limiting guest WiFi bandwidth.
- Acts by adjusting local QoS policies and choosing the best WAN paths based on current conditions.
- Learns that this specific mix of traffic patterns predicts POS latency issues, allowing for preventive measures during future events.
The intent is defined once: “POS transactions always receive priority during business hours.” It is maintained automatically across all locations without manual input, even as conditions change.
While this scenario showcases the full vision, some parts are deployable today by progressively enhancing existing SD-WAN infrastructure.
The path forward: Evolution, not revolution
Transforming network architecture is a journey, not a destination. Vision must be tempered with pragmatism. AI-agent architectures introduce real complexity: edge devices need more computational power, distributed agents require coordination mechanisms, and the agents themselves can become attack vectors.
However, these are not insurmountable challenges but rather design constraints that determine the course of evolution. A practical approach would be to work through three stages:
Phase 1 – Augmented Intelligence (Available Now)
AI agents guide human operators, highlighting anomalies and suggesting optimizations. This phase helps you build confidence in AI capabilities while maintaining full control.
Phase 2 – Bounded Autonomy (Emerging)
The agents react to specific and well-understood situations automatically, optimize traffic for recognized patterns, fail over for downtime, and escalate for new situations. This is the phase that most of today’s enterprises find themselves entering.
Phase 3 – Full Distribution (Future)
Agents work end-to-end with the highest level of intent-driven supervision, always learning and self-optimizing over the entire fabric. These emerging areas are evolving fast in the vendor’s roadmaps and labs.
It is an evolution to be guided thoughtfully.
The choice ahead
The challenge for network architects and engineers isn’t whether networked AI will become a reality, but rather how soon we can integrate this technology responsibly. As our networks continue to grow in scale and sophistication, the shortcomings of human-controlled management will become more and more evident.
Autonomous agency is more than optimization. It’s becoming an operational necessity. Networks must evolve from tools we configure into systems that understand what we’re trying to achieve.
The future of networking isn’t about controlling more devices—it’s about orchestrating intent within a network intelligent enough to execute it.
How are you preparing your network for the future? Share your thoughts in the comments.

