
A new Lua-based malware, called LucidRook, is being used in spear-phishing campaigns targeting non-governmental organizations and universities in Taiwan.
Cisco Talos researchers attribute the malware to a threat group tracked internally as UAT-10362, who they describe as a capable adversary “with mature operational tradecraft.”
LucidRook was observed in attacks in October 2025 that relied on phishing emails carrying password-protected archives.
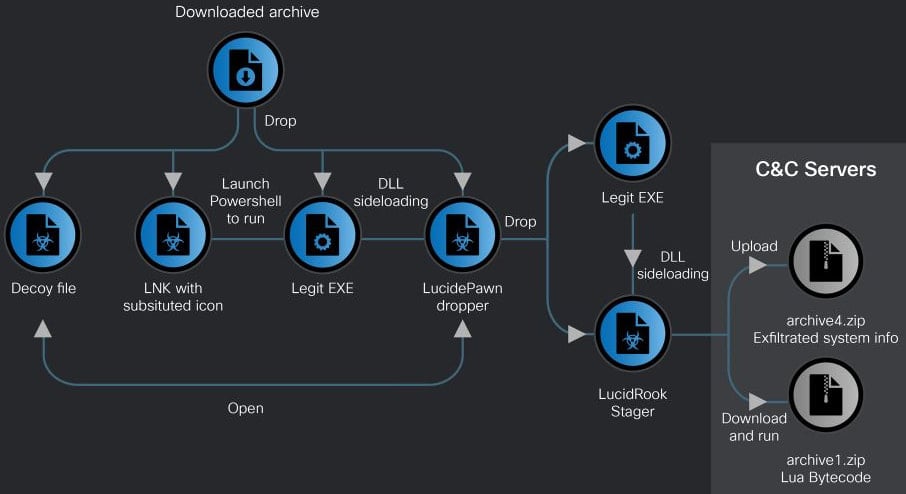
The researchers identified two infection chains, one using an LNK shortcut file that ultimately delivered a malware dropper called LucidPawn, and an EXE-based chain that leveraged a fake antivirus executable impersonating Trend Micro Worry-Free Business Security Services.
The LNK-based attack employs decoy documents, such as government letters crafted to appear as if they originate from the Taiwanese government, to divert the user’s attention.
Source: Cisco Talos
Cisco Talos observed that LucidPawn decrypts and deploys a legitimate executable renamed to mimic Microsoft Edge, along with a malicious DLL (DismCore.dll) for sideloading LucidRook.
LucidRook is notable for its modular design and built-in Lua execution environment, which allows it to retrieve and execute second-stage payloads as Lua bytecode.
This approach enables operators to update functionality without modifying the core malware, while also limiting forensic visibility. This stealth is further increased by extensive obfuscation of the code.
“Embedding the Lua interpreter effectively turns the native DLL into a stable execution platform while allowing the threat actor to update or tailor behavior for each target or campaigns by updating the Lua bytecode payload with a lighter and more flexible development process,” Cisco Talos explains.
“This approach also improves operational security, since the Lua stage can be hosted only briefly and removed from C2 after delivery, and it can hinder post-incident reconstruction when defenders recover only the loader without the externally delivered Lua payload.”
Talos also notes that the binary is heavily obfuscated across embedded strings, file extensions, internal identifiers, and C2 addresses, complicating any reverse-engineering efforts.
During its execution, LucidRook performs system reconnaissance, collecting information such as user and computer names, installed applications, and running processes.
The data is encrypted using RSA, stored in password-protected archives, and exfiltrated to attacker-controlled infrastructure via FTP.
While examining LucidRook, Talos researchers identified a related tool named “LucidKnight,” which is likely used for reconnaissance.
One notable characteristic of LucidKnight is its abuse of Gmail GMTP to exfiltrate collected data, suggesting that UAT-10362 maintains a flexible toolkit to meet varying operational needs.
Cisco Talos concludes with medium confidence that the LucidRook attacks are part of a targeted intrusion campaign. However, they were unable to capture a decryptable Lua bytecode fetched by LucidRook, so the specific actions taken post-infection aren’t known.



