[ad_1]
According to IBM’s Cost of a Data Breach 2025 report, the average cost of a corporate data breach in the United States was $10.22 million, up 9 percent from 2024, due to higher regulatory fines and detection and escalation costs. Data breaches disrupt operations, often resulting in loss of data, harm to organizational reputation, fines, and significant costs to restore systems and recover.
Data breaches remind us of the importance of cyber resilience as an essential element of survivability and continuity of operations for all organizations, especially those operating mission-essential systems, high-value systems, and/or critical assets. Resilience is also critical to reducing the costs associated with security breaches as well as minimizing damage to mission-essential systems caused by adverse events. This post highlights an approach to using data analytics as a “force multiplier” for cyber resilience, and it suggests best practices to help organizations gain situational awareness on their current security posture. It also provides guidance for tailoring resilience efforts to enhance an organization’s ability to anticipate, withstand, recover from, and adapt to evolving threats.
A Practical Approach to Cyber Resilience
Cybersecurity is often thought of as keeping the attackers out or simply stopping an attack. Framing the problem in all-or-nothing terms accepts unbounded risk and consequence once a boundary is breached. A resilience-focused approach helps organizations develop the ability to anticipate, withstand, recover from, and adapt to adverse events. Standard practices such as configuring security settings, undertaking periodic vulnerability scans, and timely patch management address obvious weaknesses. But these measures alone do not constitute a sufficient or unified approach to cybersecurity. An inconsistent implementation of security controls often requires security administrators to rely on experience over formal guidance as well as cycles of preparation driven by inspections or audits. Organizational leaders should instead work to develop a structured hardening framework to push security efforts toward a consistent, proactive approach. This blog post illustrates how a diverse array of existing guidelines and resources can be brought to bear to enhance resilience.
The Defense Information Systems Agency (DISA) has published Security Technical Implementation Guides (STIGs) and Security Requirement Guides (SRGs), These provide an important step to address the gap. The STIGs provide detailed guidance for the configuration of applications, databases, operating systems, and network devices, while SRGs tackle security requirement frameworks that align to federal standards. Both STIGs and SRGs are publicly available resources that have a control mapping structure aligning with NIST SP 800-53 Security and Privacy Controls for Information Systems and Organization and NIST SP 800-171 Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations. While designed for the Department of War, these guides can help any organization develop a measurable and standardized security posture.
Cyber Resilience Implementation: An Organizational Case Study
In this case study, an organization responsible for managing and maintaining critical infrastructure systems has been utilizing their asset inventory to identify applicable STIGs and SRGS. For purposes of this example, they use the following hardware and software and associated STIGs and SRGs:
| Hardware/Software | Required STIG/SRG Name |
|---|---|
| Windows 11 | Microsoft Windows 11 STIG |
| Mozilla Firefox Browser | Mozilla Firefox STIG |
| Microsoft Defender Endpoint | Microsoft Defender for Endpoint STIG |
| Juniper Router | Juniper Router STIG |
| Windows Defender Firewall | Windows Defender Firewall with Advanced Security STIG |
| Intrusion Detection and Prevention System | Intrusion Detection and Prevention System SRG |
| Virtual Private Network (VPN) | Virtual Private Network (VPN) SRG |
| Network Policy | Network Infrastructure Policy STIG |
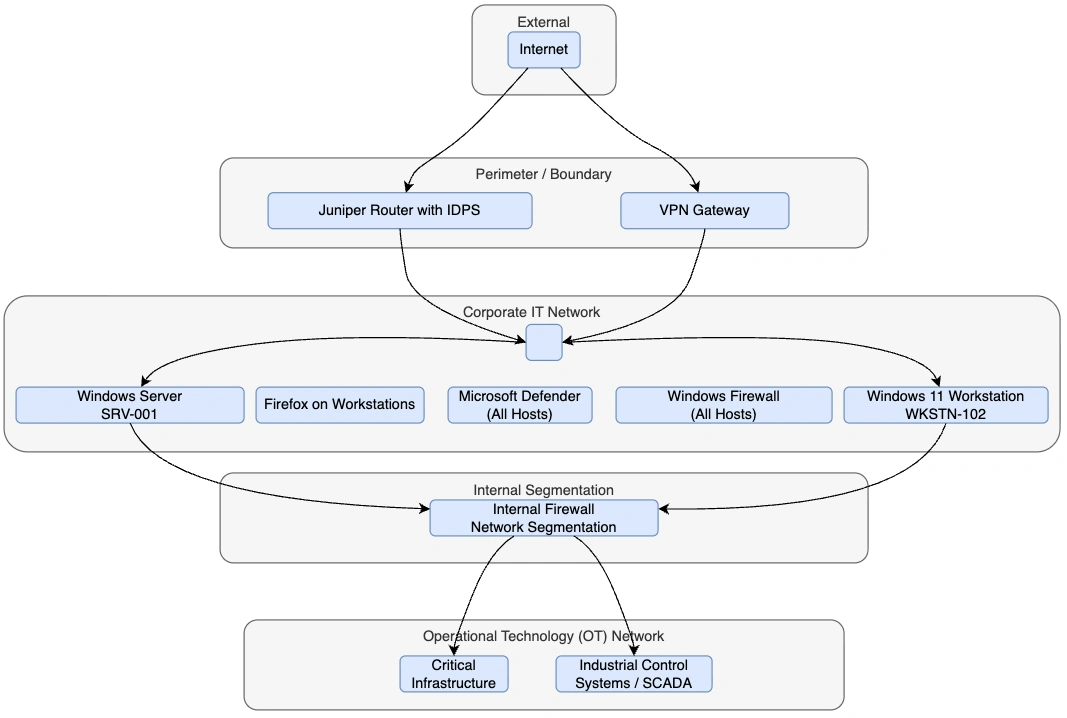
Figure 1: This figure details a high-level cybersecurity and network architecture for the organization, showing how the different systems are connected and protected across layers.
The organization downloaded the required STIGs and SRGs from the official DoW Cyber Exchange. Additionally, they downloaded the Security Content Automation Protocol (SCAP) Compliance Checker and STIG Viewer application from the same website.
- STIG Viewer Application allows users to view and manage the STIG and SRG checklists to assess and implement security controls, analyze compliance, and document findings.
- The Security Content Automation Protocol (SCAP) is a suite of “interoperable specifications for the standardized expression, exchange, and processing of security configuration and vulnerability information. SCAP enables consistent automation and reporting across products and environments by defining machine-readable content and associated processing requirements.”
After installing the SCAP Compliance Checker, the organization’s Information System Security Officer (ISSO) and members of the security team created a new scan, importing the STIG and SRG files before selecting the correct security profile. The scan is a standardized method to check systems based on compliance with security configurations, known vulnerabilities, and policy violations. The security profile selection option assists in choosing which rules are scanned and includes full compliance scanning and tailored versions based on system classifications.
Once completed, the security team saved the results of the scan as a .ckl file to easily import it into STIG Viewer. With the tool, the ISSO could now view compliance failures within the system and the severity of the failure associated with the STIG or SRG rule. Additionally, the scan provides a status indicator for each finding to signal whether the scan was successful, if the system is in compliance, or if the finding was not reviewed. Some findings are not automatically reviewed and required manual review by the system administrators, which was done by reviewing the documentation in the STIG or SRG that includes the check instructions for assessing compliance.
Once the STIGs and SRGs were mapped to the asset inventory and the assessment was completed, the artifacts were integrated into an operational dashboard with system criticality ratings, compliance data, and patch metrics. The Center for Internet Security (CIS) Critical Security Controls V7 Measures and Metrics guide is a practical resource that provides more than 100 actionable metrics as well as benchmark targets and step-by-step guidance to help organizations measure and improve patch management and SCAP-based vulnerability management. The security team was able to analyze this data to track deviations while also allowing security architects to define baseline configurations in concert with the organization’s cybersecurity strategy. Additionally, hardened images of endpoints and servers were created based on the STIG findings and implementation guidance. These images enable baseline consistency across devices by using the preconfigured system images. They also allow the security team to start with an already approved hardened baseline system when adding new systems, instead of starting from scratch.
While this approach creates a strong security foundation, it lacks sufficient data to identify trends and areas of elevated risk. As historical STIG compliance data accumulates, the security team is able to strengthen enterprise protection by applying complex analytics to enable more proactive identification and mitigation of risks. At the diagnostic level, the team identifies root causes of configuration drift by correlating recurring misconfigurations, such as failures, to enforce baseline settings (e.g., disabled audit logging or unauthorized access control configuration changes) with change logs and deployment pipelines (i.e., the processes used to build, test, and release system updates). These diagnostic analytics allow the team to transition to predictive analytics, forecasting future risk introduced by inconsistent image management and undocumented administrative overrides.
Additionally, the security team was able to combine STIG and SRG non-compliance severity using the CAT levels severity classification system:
- CAT I represents the highest risk vulnerabilities (critical).
- CAT II indicates moderate risk.
- CAT III reflects lower risk findings.
Use of the CAT levels, when combined with CISA’s Known Exploited Vulnerabilities (KEV) catalog and asset exposure data, results in a weighted risk scoring model. The security team discovered that only a small percentage of systems accounted for the majority of risk. The organization was then able to prioritize hardening, monitoring, and segmentation efforts based on predicted likelihood and business impact rather than responding to alerts after compromise attempts.
As these processes matured, the organization evolved to more proactive resilience engineering by mapping high-risk STIG and SRG failures to MITRE ATT&CK techniques. This practice identified how configuration weaknesses influenced risk while also enabling attack-path modeling and lateral movement probability. This insight allowed the organization to make targeted improvements to authentication controls, privilege boundaries, and logging standards to reduce the attack paths to critical assets.
Next Steps: Maturing Organizational Analytics Capabilities
As illustrated by our case study, the application of data analytics significantly improves resilience and survivability by enabling organizational leaders to make decisions based on data and data analytics. The types of analytics include descriptive analytics (understanding what has happened), diagnostic analytics (explaining why it happened), predictive analytics (anticipating what is likely to happen), and prescriptive analytics (recommending what actions should be taken). As an organization’s analytics capability matures, it can reduce and better define accepted risk.
Through the structured use of STIGs and SRGs combined with data-driven analytics, the organizational leaders were able to transition from reactive compliance management to a measurable, intelligence-driven resilience strategy capable of predicting threats by identifying weaknesses before they can be exploited and establishing preemptive standard actions. A key part of any resilience strategy involves data that is accurate, timely, and able to directly inform risk postures (e.g., asset criticality, vulnerability severity, exposure, and configuration drift).
A cyber resilience strategy that focuses on refining data analytics and allocating resources based on the greatest risk enables organizations, especially in resource-constrained environments, to maximize the impact of security efforts while efficiently utilizing resources. This approach means moving resiliency further left in the process by prioritizing resilience in design decisions and operational planning and allowing teams to act proactively rather than reactively. It also enables faster detection of adverse events while increasing the effectiveness of response actions, resulting in fewer cascade failures, reduced downtime, and lower costs associated with an incident.
[ad_2]
Source link

